- +1 (628)-432-1595
- reach@techdatapark.com
- 3080 Olcott St D205, Santa Clara, CA 95054, United States
Cybersecurity has become one of the highest-priority investment areas for businesses worldwide. From ransomware protection and endpoint defense to cloud security, compliance, identity management, and threat monitoring, organizations are actively searching for reliable vendors and solutions. This creates major opportunities for companies selling cybersecurity products or services.
A targeted Cybersecurity Email List helps your business reach verified decision-makers responsible for evaluating and purchasing security solutions. Instead of relying on broad or outdated databases, you can connect directly with CISOs, CIOs, IT Directors, Security Managers, Risk Officers, and other high-value contacts who influence buying decisions.
With the right Cybersecurity Email List, your marketing and sales teams can generate better conversations, improve response rates, shorten sales cycles, and scale pipeline growth more efficiently. TechDataPark helps businesses achieve this with accurate, segmented, and campaign-ready B2B data.


















A Cybersecurity Email List is a verified business database containing companies and professionals involved in information security, cloud protection, compliance management, endpoint security, risk reduction, and cyber defense initiatives.
This type of list helps businesses reach people who actively manage cybersecurity budgets, vendor relationships, infrastructure security, employee awareness tools, data privacy programs, and compliance frameworks.
Typical contacts in a Cybersecurity Email List include:
Companies use a Cybersecurity Email List for B2B lead generation, webinar invites, product demos, partnerships, account-based marketing, and regional expansion campaigns.

Traditional prospecting methods often consume valuable time, budget, and internal resources. Many generic databases include outdated contact details, irrelevant job roles, or individuals without decision-making authority. This leads to poor campaign performance and wasted outreach efforts. A well-segmented Cybersecurity Email List helps your team focus on verified prospects who are more likely to engage, evaluate solutions, and influence purchasing decisions.
Quickly connect with verified cybersecurity buyers instead of spending weeks researching accounts manually. This helps your SDR and sales teams fill pipelines faster and spend more time closing opportunities rather than prospecting.
Segment contacts by job title, industry, geography, company size, revenue, or technology environment. Better segmentation allows more personalized campaigns that speak directly to each buyer’s specific security challenges.
Relevant outreach often improves open rates, click rates, replies, booked meetings, and conversions. By targeting qualified prospects, businesses can reduce wasted spend and improve overall marketing efficiency.
Sales teams spend more time selling and less time searching for prospects. Accurate data helps reps prioritize high-value accounts and focus on conversations that matter most.
Instead of filling your CRM with low-fit leads, a refined Cybersecurity Email List helps generate prospects that match your ideal customer profile, increasing the chances of meaningful opportunities.
If you are launching a new cybersecurity product or service, targeted data helps you reach the right audience quickly and build awareness faster than broad prospecting methods.
Many older databases are no longer effective in today’s market. Buyers expect relevant communication, and spam filters are more advanced than ever. Poor-quality lists create low engagement and damage sender reputation.
Common issues include:
A modern Cybersecurity Email List should be refreshed regularly, verified carefully, and designed for precision targeting.
A B2B cybersecurity contact database is a verified collection of decision-maker contact information curated specifically for companies selling security products and services. Unlike newsletter subscriptions, this type of list is built for outbound prospecting, account-based marketing, and cold outreach.
Sales teams use cybersecurity contact databases to identify accounts showing buying signals. Marketing teams leverage the same data for targeted campaigns, webinar promotions, and multi-channel ABM programs.
When evaluating Cybersecurity Email List Providers, TechDataPark delivers unmatched value, accuracy, and performance.
With these capabilities, TechDataPark stands as the most trusted partner for acquiring a high-quality Cybersecurity email database.
A well-structured Cybersecurity Email List is a powerful asset for B2B marketers looking to connect with the right audience at the right time. It enables precise targeting, improves engagement, and helps businesses generate high-quality leads while maximizing ROI across email, ABM, and multi-channel campaigns.
Reach professionals from information security companies using advanced segmentation by role, industry, and technology, ensuring your campaigns connect with the most relevant audience.
Identify and engage prospects actively researching or investing in cybersecurity solutions, helping your sales team focus on opportunities with higher conversion potential.
Leverage firmographic and technographic insights to personalize messaging, increasing engagement, response rates, and overall campaign performance across multiple channels.
Access Cybersecurity companies in USA and across global markets, enabling you to expand your outreach, enter new regions, and scale your B2B marketing efforts effectively.
Perfect for account-based marketing, allowing you to target key decision-makers within specific companies and build personalized, high-value engagement strategies.
Connect directly with decision-makers like CISOs and IT leaders, reducing sales cycles and accelerating deal closures through direct and meaningful interactions.
A well-structured Cybersecurity Leads Database is a valuable asset for businesses across industries, helping them identify, target, and engage decision-makers effectively while improving lead quality, campaign performance, and overall B2B marketing ROI.
A high-quality Cybersecurity Email List supports multiple growth channels across marketing, sales, partnerships, and business development. Instead of relying on broad outreach, businesses can use verified data to reach decision-makers already involved in cybersecurity planning, compliance, risk management, and technology purchasing.
With the right audience, your campaigns become more relevant, more personalized, and more effective.

Promote product launches, security assessments, consultations, whitepapers, case studies, audits, newsletters, and webinars. A targeted audience often improves engagement and lead quality.
Book meetings with CISOs, CIOs, CTOs, IT Directors, and security leaders who may be evaluating vendors, services, or new technologies.
Invite relevant contacts to live demos, executive briefings, online events, threat intelligence sessions, and virtual roundtables focused on cybersecurity trends.
Connect with MSSPs, MSPs, VARs, resellers, system integrators, and consultants looking for strategic cybersecurity solutions to offer their clients.
Cross-sell or upsell related services such as compliance tools, cloud security, endpoint protection, identity management, or monitoring solutions to security-focused accounts.
Enter new industries, regions, or countries using accurate and segmented data. This helps businesses scale into fresh markets with localized outreach strategies.
Help SDR and BDR teams build stronger pipelines by reaching qualified accounts that match your ideal customer profile.
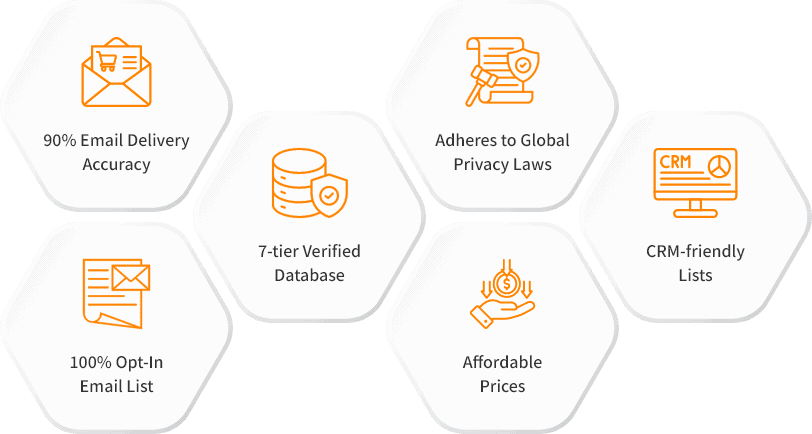
Over 5,000 businesses worldwide trust our verified B2B database to connect with the right decision-makers, engage high-value prospects, and close deals faster. With our 7-tier verification process, you get accurate and up-to-date contact lists tailored to your target industry, location, or technology stack.
From startups to Fortune 500 companies, our clients use our data to boost response rates, shorten sales cycles, and maximize ROI. Whether you are running email campaigns, account-based marketing, or cold calling, the right data puts you ahead of the competition. It’s time to power your growth with the same trusted resource industry leaders use every day. So, why are you still hesitating? Grab our technology users email list now and stay ahead of your competitions!
Getting started with a Cybersecurity Email List is simple when you have a clear audience and quality data. A strategic approach helps improve campaign performance, reduce wasted outreach, and generate stronger business opportunities.
1. Define Your Audience
Choose the industries, countries, company sizes, revenue ranges, and job titles you want to target. You can also narrow your audience by seniority level, department, or specific cybersecurity interests to match your ideal customer profile.
2. Review Free Sample Data
Evaluate contact quality, formatting, accuracy, relevance, and campaign readiness before moving forward. Reviewing a sample helps ensure the data aligns with your business goals and outreach strategy.
3. Launch Smarter Campaigns
Use your Cybersecurity Email List across email marketing, SDR outreach, ABM campaigns, LinkedIn prospecting, webinar invitations, and event promotions. Well-targeted campaigns often lead to stronger engagement and better ROI.
Pricing varies based on list size, customization requirements, and data attributes included. Most providers offer custom quotes based on targeting criteria and volume.
A cybersecurity newsletter delivers curated news content to subscribers. A B2B contact list is a database of verified professional emails used for sales and marketing outreach.
Quality providers refresh data every 30 to 90 days to remove outdated records, job changes, and invalid emails. TechDataPark updates lists every 45 days.
Yes, reputable providers allow filtering by job title, seniority, department, employee count, revenue, geography, and technology stack.
A verified list from a quality provider typically delivers 90%+ inbox placement rates, significantly higher than unverified sources.
Yes, when sourced from compliant providers who collect opt-in consent and adhere to regulations like GDPR, CCPA, and CAN-SPAM.
Common targets include CISO, VP of Security, IT Security Director, Security Operations Manager, Network Security Engineer, and Compliance Officer.
Most providers deliver data in CSV or Excel formats that import directly into CRMs like Salesforce, HubSpot, or marketing automation platforms.
You can obtain accurate technology users email addresses from reputable B2B data providers who verify their databases through multi-step processes. This ensures you’re reaching valid contacts and reduces bounce rates for your campaigns.